Introduction
In 2018, I discovered a vulnerability within the ‘Saved’ option on Facebook, allowing me to break my saved items. Since the impact was limited to my own account, I refrained from reporting it to the Facebook Security Team, considering it non-applicable (N/A) similar to finding a ‘Self XSS.’ In 2019, I revisited the issue and found a method to escalate it into a valid bug by leveraging another feature within the ‘Saved’ option, known as ‘Collection.’ For more details about ‘Saved’ and ‘Collection,’ refer to https://www.facebook.com/help/503872743411567?helpref=related.
The finding
In the ‘Collection’ feature, you can designate your friends as ‘Contributors.’ Breaking your saved option will consequently impact their saved options since they have permission on your broken collection.
While this bug may appear to be a ‘DOS’ (Denial of Service) issue, the best explanation for this behavior was articulated by Philippe Harewood (PHWD). In his words, ‘the bug limits the usability of certain users based on unhandled input, leading to errors in the app making it unresponsive.’
To put it plainly, a malicious user could exploit this vulnerability to prevent users from viewing their saved items on https://www.facebook.com/saved/. This adds an element of disruption and potential inconvenience to affected users.
Reproduction Steps
Step 1: (Attacker) Creating a Collection
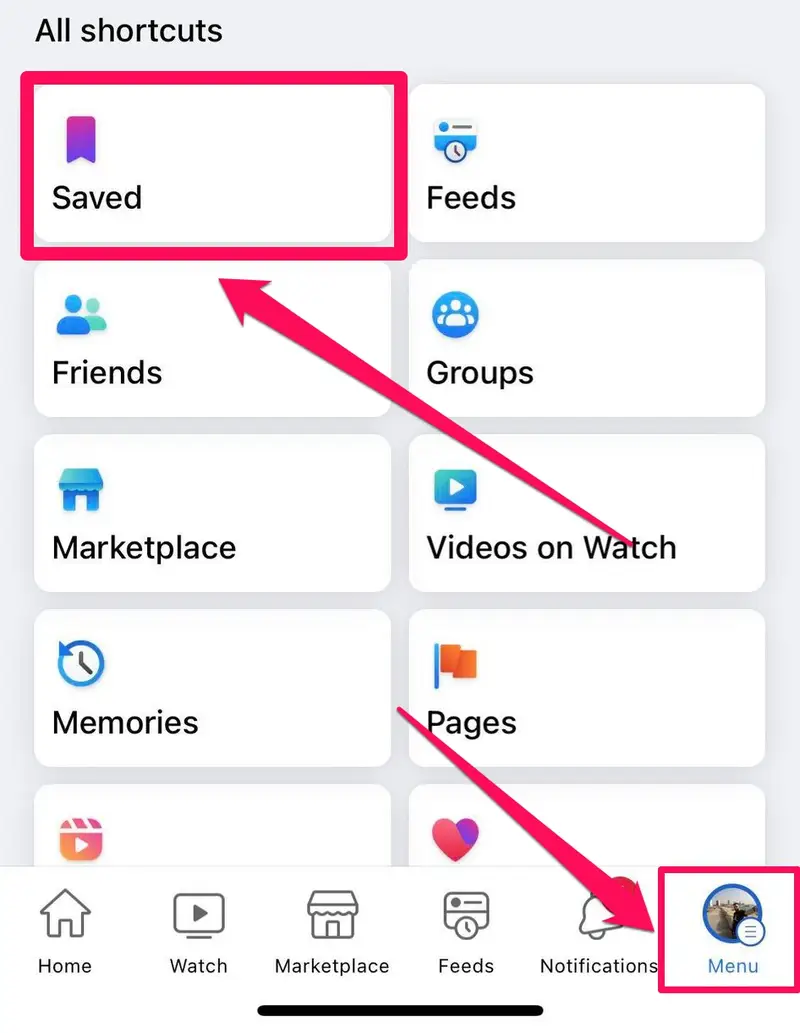
- The attacker browses to their saved items on https://www.facebook.com/saved/.
- They create a new collection by navigating to the ‘New Collection’ option, entering any name, and selecting ‘Create.’
Step 2: (Attacker) Adding Victim to Collection
- The attacker adds their friend (Victim) to the collection by visiting https://www.facebook.com/saved/.
- They select the previously created Collection Name, click on ‘Add Contributors,’ and type the victim’s name.
Step 3: (Attacker) Saving a Random Post to Collection
- The attacker goes to any random post, clicks on the three dots option, selects ‘Save Post,’ and is redirected to https://www.facebook.com/saved/.
- From the saved items, they click on “Add to a Collection,” intercept the request with Burpsuite, and choose the previously created collection.
Step 4: (Attacker) Manipulating the Post Request
- The attacker observes a post request similar to the following:
POST /save/list/mutate/ HTTP/1.1
Host: www.facebook.com
action=SAVE_IN_EXISTING_LIST&mechanism=add_to_list_button&surface=save_dashboard&list_id=111111&object_id=22222&__user= ......etc
2.The attacker copies the value of “list_id=” and pastes it on the “object_id” value, making both values identical:
list_id=111111&object_id=111111
3.
- They forward the manipulated request to the server, receiving a 200 OK response.
Step 5: (Victim) Unable to Access Saved Items
- When the victim browses to their saved items on https://www.facebook.com/saved/, they encounter an error message:
"Sorry, something went wrong. We're working on getting this fixed as soon as we can."
The victim is no longer able to see their saved items.
Timeline
- Sarmad 01 May 2019
- Initial Report
- Meta Bug Bounty 03 May 2019
- Report Triaged
- Meta Bug Bounty 24 Jun 2019
- Bug Fixed
- Sarmad 24 Jun 2019
- Fixed Confirmed
- Meta Bug Bounty 02 Jul 2019
- Bounty Awarded